

The Qilin ransomware group has stolen data from Die Linke, a German democratic socialist political party, and is threatening to leak it.
On March 27, a day after the threat actor compromised its network, the party disclosed a cyber incident but stopped short of confirming a data breach.
Founded in 2007, the Die Linke (Left Party) is currently represented in the German parliament (Bundestag) through 64 members. It has 123,000 registered members and participates in several state governments, especially in eastern Germany.
“According to current findings, the attackers aim to publish sensitive data from the internal areas of the party organization as well as personal information of employees at the party headquarters,” Die Linke says.
“It is currently unclear whether and to what extent this has succeeded or has already occurred. However, such a risk exists.”
The party clarified that its membership database wasn’t impacted, specifically stating that the attackers failed in their effort to obtain member data.
Die Linke said that it received information that behind the attack is the Qilin ransomware group, describing the threat actor as Russian-speaking cybercriminals that are both financially and politically motivated. The German party also said that the attack on its systems “does not appear to be coincidental in this context.”
“Such digital attacks, and ransomware use in particular, are often part of hybrid warfare and constitute an attack on critical infrastructure,” commented the party.
On April 1st, Qilin claimed the attack on Die Link publicly, adding it to the list of victims on its data leak site without publishing any data samples.
Threatening to publish stolen data is a standard pressure tactic to coerce victims into paying a ransom.
Die Linke has notified the German authorities and filed a criminal complaint with the police. Additionally, the party is working with independent IT experts to help them safely restore impacted systems.
Russia-linked threat actors have targeted political parties in Germany in the past. In 2024, Mandiant uncovered a campaign from APT29 targeting CDU, a major political party in the country, with a backdoor named WineLoader.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

In February 2026, the University of Mississippi Medical Center (UMMC) fell victim to a ransomware attack. The incident took the Epic electronic health record system offline across 35 clinics and more than 200 telehealth sites, forcing the cancellation of chemotherapy appointments and the postponement of non-emergency surgeries. Medical staff were required to revert to paper-based workflows, leaving countless patients to bear the consequences.
UMMC is far from an isolated case. According to recent data, 93% of U.S. healthcare organizations experienced at least one cyberattack in 2025, and 72% of respondents reported that at least one incident directly disrupted patient care.
The manufacturing and financial sectors are equally exposed. In February 2026, payment processing network BridgePay suffered a ransomware attack that took its APIs, virtual terminals, and payment pages completely offline. Across all industries, publicly disclosed ransomware attacks surged 49% year-over-year in 2025, reaching 1,174 confirmed incidents.
As hospitals halt treatments, financial institutions freeze transactions, and manufacturers shut down production lines, ransomware has firmly established itself as a direct business risk with tangible operational consequences.
Early ransomware operated on a straightforward premise: infiltrate a system, encrypt files, and demand payment in exchange for the decryption key. As organizations began countering this tactic by restoring from backups rather than paying ransoms, threat actors responded by developing a more lucrative model — double extortion.
In a double extortion attack, adversaries first exfiltrate sensitive files — such as patient records and billing data — before encrypting the target system. Victims are then pressured on two fronts: pay to receive the decryption key, or face public exposure of the stolen data.
Backups alone are insufficient against this model. Since attackers already possess the data, refusing to pay the ransom can result in the public release of sensitive files, exposing organizations to significant business losses and regulatory consequences.
The threat landscape has continued to escalate, with triple extortion cases on the rise — a tactic in which attackers directly contact a victim organization's customers or partners to apply additional pressure.
As of 2025, 124 active ransomware groups have been identified, 73 of which are newly emerged.
The proliferation of AI-powered tools has lowered the barrier to entry for cybercrime, making ransomware capabilities increasingly accessible to less sophisticated actors.
D.AMO makes stolen data unreadable.
See how D.AMO defends against every stage of a ransomware attack.
Learn MoreThe rise of multi-extortion ransomware fundamentally changes the assumptions underlying traditional defense strategies. Perimeter-based prevention alone is no longer sufficient.
Organizations need a security posture that protects data from being weaponized after a breach — rendering exfiltrated data unreadable, blocking ransomware from accessing files in the first place, and enabling rapid recovery even when an attack succeeds.
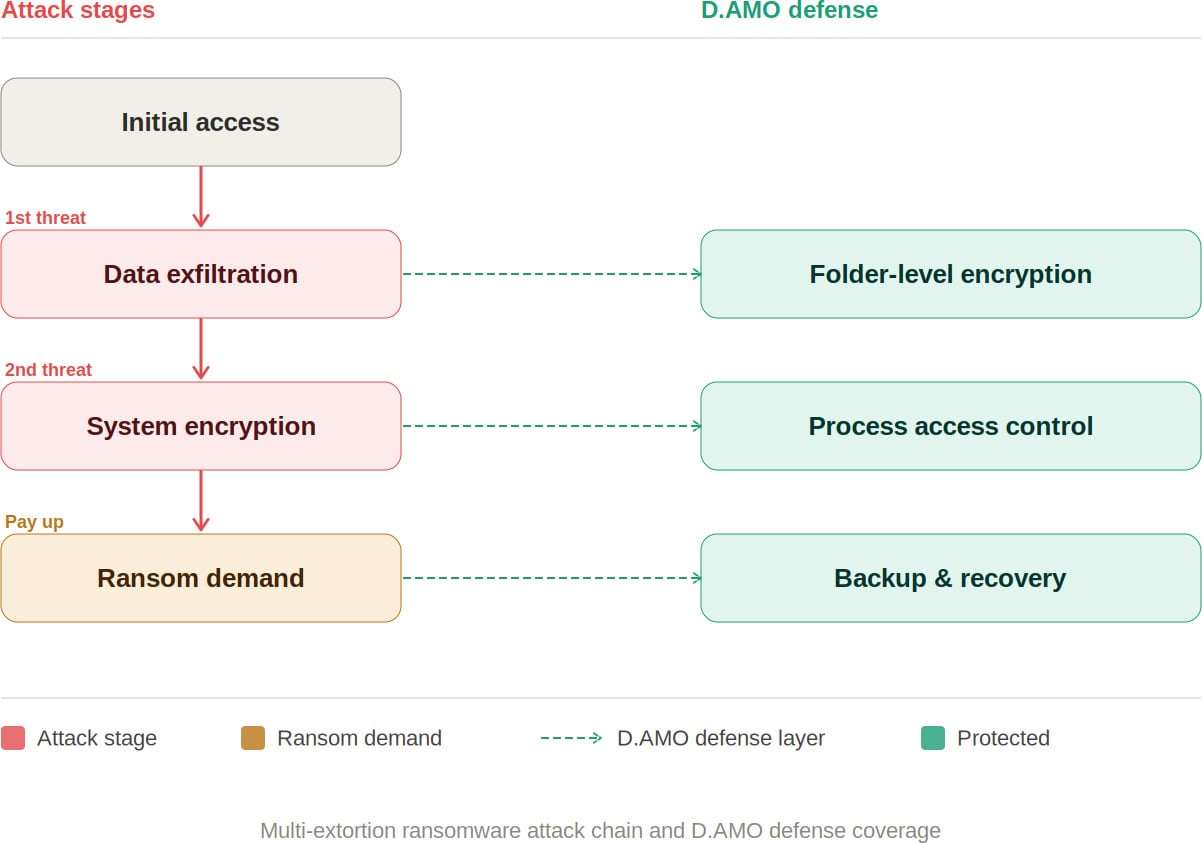
D.AMO, developed by Penta Security, is an encryption-based data protection platform designed to address every phase of a multi-extortion ransomware attack. It delivers integrated encryption, access control, and backup recovery across on-premises and cloud environments.
By applying file encryption and process-based access control technologies, D.AMO protects critical data stored on servers and PCs — safeguarding sensitive information against malicious programs through robust access enforcement. D.AMO's key capabilities are as follows:
Folder-Level File Encryption
D.AMO KE encrypts all files within administrator-designated folders at the OS level. Deployable via an installer without source code modification, it operates using kernel-level encryption technology, enabling fast and secure encryption on existing systems with no disruption to the user experience.
Encryption policies are applied at the folder level, ensuring consistent protection with minimal operational overhead. Critically, even if an attacker exfiltrates sensitive data, the files remain encrypted — neutralizing the data exposure threat that is central to double extortion.
D.AMO KE enforces strict access control over processes and OS users, permitting only explicitly authorized access. Ransomware and other malicious applications are automatically blocked from accessing encrypted folders, preventing unauthorized file manipulation.
All blocked activity is recorded through an audit log function and can be reviewed centrally via D.AMO Control Center.
Even in the event of a successful attack, organizations can resume operations through an independently managed recovery system. With D.AMO in place, the ability to restore from backup significantly reduces dependence on decryption key negotiations with threat actors.
As multi-extortion tactics become the norm, neutralizing the data attackers seek to exploit has become a strategic priority. Organizations need the ability to render exfiltrated data unreadable, prevent ransomware from accessing files, and recover rapidly when incidents occur.
D.AMO addresses each stage of a ransomware attack within a single integrated platform — combining encryption, process-based access control, and backup recovery into a unified line of defense.
Want to learn more? Download the D.AMO Data Sheet.
Sponsored and written by Penta Security.
html Sponsored by Penta Security 1775215520 Microsoft still working to fix Exchange Online mailbox access issues https://www.bleepingcomputer.com/news/microsoft/microsoft-still-working-to-fix-exchange-online-mailbox-access-issues/
Microsoft is investigating and working to resolve Exchange Online mailbox access issues that have intermittently affected Outlook mobile and macOS users for weeks.
When it first acknowledged this service issue (tracked under EX1256020) last week, Microsoft said it started on March 11 and that the root cause was a newly introduced virtual account. While the company flagged it as resolved on April 1, the incident has been re-added to the admin message center under a different tag (EX1268771).
"We've received reports from affected tenants that the impact scenario originally communicated through SHD EX1256020 is still ongoing. We're working to restart the Notification Broker service on affected portions of Exchange Online service infrastructure to remediate impact while we continue our analysis into the underlying root cause," Microsoft says.
"Impact may occur intermittently for some users accessing their Exchange Online mailboxes in the Outlook mobile apps or the new Outlook for Mac desktop client. This section may be updated as our investigation progresses."
In the latest update issued on Thursday evening, the Exchange Online team said it's still investigating the root cause and working on additional measures to prevent this issue from recurring.
While Microsoft has yet to share which regions or how many users have been affected by this issue over the last three weeks, it flagged this as an incident, which typically applies to critical service issues with noticeable user impact.
Earlier this month, Microsoft mitigated an Exchange Online outage that prevented users from accessing mailboxes and calendars via Outlook on the web, Outlook desktop, Exchange ActiveSync, and other Exchange Online connection protocols.
The same day, it fixed a separate issue that caused Office.com or Microsoft 365 Copilot web sign‑in problems affecting the Microsoft Copilot desktop app, Copilot in Microsoft Teams, and Copilot in Office apps.
Another Exchange Online service outage that intermittently blocked email via the Internet Mailbox Access Protocol 4 (IMAP4) was addressed in January, while a similar incident blocked Exchange Online access via the classic Outlook desktop client in November.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

A former core infrastructure engineer has pleaded guilty to locking Windows admins out of 254 servers as part of a failed extortion plot targeting his employer, an industrial company headquartered in Somerset County, New Jersey.
According to court documents, 57-year-old Daniel Rhyne from Kansas City, Missouri, remotely accessed the company's network without authorization using an administrator account between November 9 and November 25.
Throughout this time, he allegedly scheduled tasks on the company's Windows domain controller to delete network admin accounts and to change the passwords for 13 domain admin accounts and 301 domain user accounts to "TheFr0zenCrew!".
The prosecutors also accused Rhyne of scheduling tasks to change the passwords for two local admin accounts, which would affect 3,284 workstations, and for two more local admin accounts, which would impact 254 servers on his employer's network. He also scheduled some tasks to shut down random servers and workstations on the network over multiple days in December 2023.
Subsequently, on November 25, Rhyne emailed a number of his coworkers a ransom email titled "Your Network Has Been Penetrated," saying that all IT administrators had been locked out of their accounts and that server backups had been deleted to make data recovery impossible.
Additionally, the emails threatened to shut down 40 random servers daily over the next ten days unless the company paid a ransom of 20 bitcoin (worth roughly $750,000 at the time).
"On or about November 25, 2023, at approximately 4:00 p.m. EST, network administrators employed at Victim-1 began receiving password reset notifications for a Victim-1 domain administrator account, as well as hundreds of Victim-1 user accounts," the criminal complaint reads.
"Shortly thereafter, the Victim-1 network administrators discovered that all other Victim-1 domain administrator accounts were deleted, thereby denying domain administrator access to Victim-1's computer networks."
Forensic investigators found that on November 22, Rhyne used a hidden virtual machine and his account to search the web for information on clearing Windows logs, changing domain user passwords, and deleting domain accounts as he planned his extortion plot.
One week earlier, Rhyne made similar web searches on his laptop, including "command line to remotely change local administrator password" and "command line to change local administrator password."
Rhyne was arrested in Missouri on Tuesday, August 27, and released after his initial appearance in federal court. The hacking and extortion charges to which he pleaded guilty carry a maximum penalty of 15 years in prison.
Earlier this month, a North Carolina data analyst contractor was found guilty of extorting his employer, Brightly Software (a Software-as-a-Service company previously known as SchoolDude), for $2.5 million.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

Starting this week, Microsoft has begun force-upgrading unmanaged devices running Windows 11 24H2 Home and Pro editions to Windows 11 25H2.
According to the company's Lifecycle Policy site, Windows 11 24H2 will reach end of support in roughly six months, on October 13, 2026.
Also known as the Windows 11 2025 Update, Windows 11 25H2 began rolling out in September to eligible Windows 10 or Windows 11 devices as a minor update installed through enablement packages less than 200 KB in size.
"The machine learning-based intelligent rollout has expanded to all devices running Home and Pro editions of Windows 11, version 24H2 that are not managed by IT departments," Microsoft said in a Monday update to the Windows release health dashboard.
"Devices running these editions will no longer receive fixes for known issues, time zone updates, technical support, or monthly security and preview updates containing protections from the latest security threats," it added.
"These devices will automatically receive the update to Windows 11, version 25H2 when they're ready. No action is required, and you can choose when to restart your device or postpone the update."
Those who don't want to wait for the automatic upgrade can manually check whether the update is available in Settings > Windows Update and click the link to download and install Windows 11 25H2.
If you're not ready to upgrade, you can also pause updates from Settings > Windows Update by selecting the amount of time you'd like to pause them. However, you must install the latest updates after the time limit has passed.
Microsoft also provides a support document and a step-by-step guide to help users resolve problems encountered during the Windows 11 25H2 upgrade process.
Since the March 2026 Patch Tuesday updates were released, Microsoft has issued several emergency updates, including one that addresses a known issue breaking sign-ins with Microsoft accounts across multiple Microsoft apps, such as Teams and OneDrive.
It also pushed out-of-band updates for hotpatch-enabled Windows 11 Enterprise devices that fixed a Bluetooth device visibility issue and security vulnerabilities in the Routing and Remote Access Service (RRAS) management tool.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

The European Union's Cybersecurity Service (CERT-EU) has attributed the European Commission cloud hack to the TeamPCP threat group, saying the resulting breach exposed the data of at least 29 other Union entities.
The European Commission publicly disclosed the incident on March 27 after BleepingComputer reached out for confirmation that the Amazon cloud environment of the European Union's main executive body had been breached.
Two days earlier, the Commission notified CERT-EU of the hack, saying that its Cybersecurity Operations Center was not alerted to API misuse, potential account compromise, or any abnormal network traffic until March 24, five days after the initial intrusion.
On March 10, TeamPCP used a compromised Amazon Web Services API key with management rights over other European Commission AWS accounts (stolen in the Trivy supply-chain attack) to breach the Commission's Amazon cloud environment.
In the next stage of the attack, they used TruffleHog (a tool for scanning and validating cloud credentials) to search for additional secrets, then attached a newly created access key to an existing user to evade detection before conducting further reconnaissance and stealing data.
TeamPCP has been linked to supply-chain attacks targeting multiple other developer code platforms, such as GitHub, PyPi, NPM, and Docker.
The cybercrime gang has also compromised the LiteLLM PyPI package in an attack that impacted tens of thousands of devices using its "TeamPCP Cloud Stealer" information-stealing malware.
On March 28, data extortion group ShinyHunters published the stolen dataset on their dark web leak site as a 90GB archive of documents (approximately 340GB uncompressed), containing names, email addresses, and email content.
CERT-EU's analysis confirmed that the threat actors have stolen tens of thousands of files containing personal information, usernames, email addresses, and email content, and that the resulting data breach potentially affects 42 internal European Commission clients and at least 29 other Union entities using the europa.eu web hosting service.
"The threat actor used the compromised AWS secret to exfiltrate data from the affected cloud environment. The exfiltrated data relates to websites hosted for up to 71 clients of the Europa web hosting service: 42 internal clients of the European Commission, and at least 29 other Union entities," CERT-EU said on Thursday.
"Analysis of the published dataset has so far confirmed the presence of personal data, including lists of names, last names, usernames, and email addresses, predominantly from the European Commission’s websites but potentially pertaining to users across multiple Union entities," it added.
"The dataset also contains at least 51,992 files related to outbound email communications, totalling 2.22 GB. The majority of these are automated notifications with little to no content. However, 'bounce-back' notifications, which are responses to incoming messages from users, may contain the original user-submitted content, posing a risk of personal data exposure."
CERT-EU added that no websites were taken offline as a result of this incident or tampered with, and no lateral movement to other Commission AWS accounts has been detected.
While the analysis of exfiltrated databases and files is ongoing and will likely require "a considerable amount of time," the Commission has notified relevant data protection authorities and is in direct communication with affected entities.
In February, the European Commission disclosed another data breach after discovering that a mobile device management platform used to manage staff's devices had been hacked.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
Threat actors are exploiting the recent Claude Code source code leak by using fake GitHub repositories to deliver Vidar information-stealing malware.
Claude Code is a terminal-based AI agent from Anthropic, designed to execute coding tasks directly in the terminal and act as an autonomous agent, capable of direct system interaction, LLM API call handling, MCP integration, and persistent memory.
On March 31, Anthropic accidentally exposed the full client-side source code of the new tool via a 59.8 MB JavaScript source map included by accident in the published npm package.
The leak contained 513,000 lines of unobfuscated TypeScript across 1,906 files, revealing the agent’s orchestration logic, permissions, and execution systems, hidden features, build details, and security-related internals.
The exposed code was rapidly downloaded by a large number of users and published on GitHub, where it was forked thousands of times.
According to a report from cloud security company Zscaler, the leak created an opportunity for threat actors to deliver the Vidar infostealer to users looking for the Claude Code leak.
The researchers found that a malicious GitHub repository published by user “idbzoomh” posted a fake leak and advertised it as having “unlocked enterprise features” and no usage restrictions.
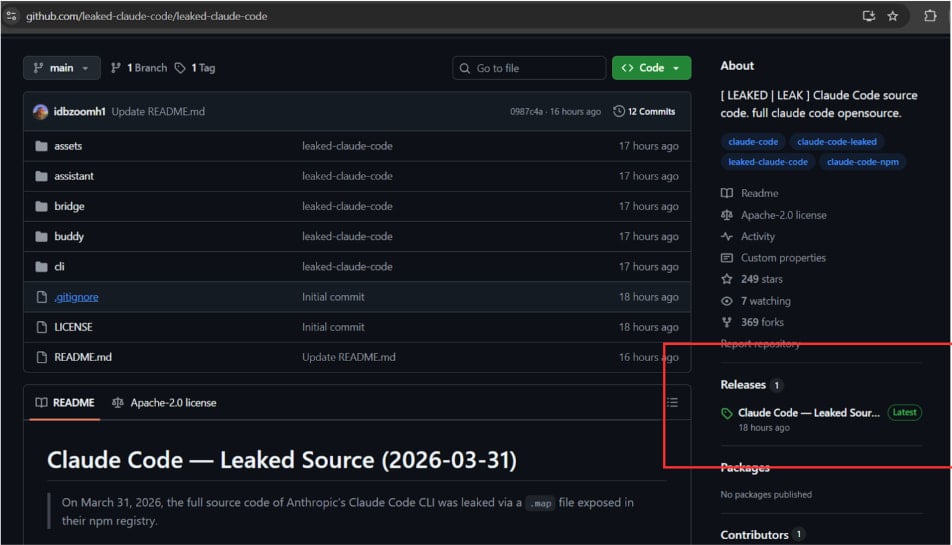
To drive as much traffic to the bogus leak, the repository is optimized for search engines and is shown among the first results on Google Search for queries like “leaked Claude Code.”
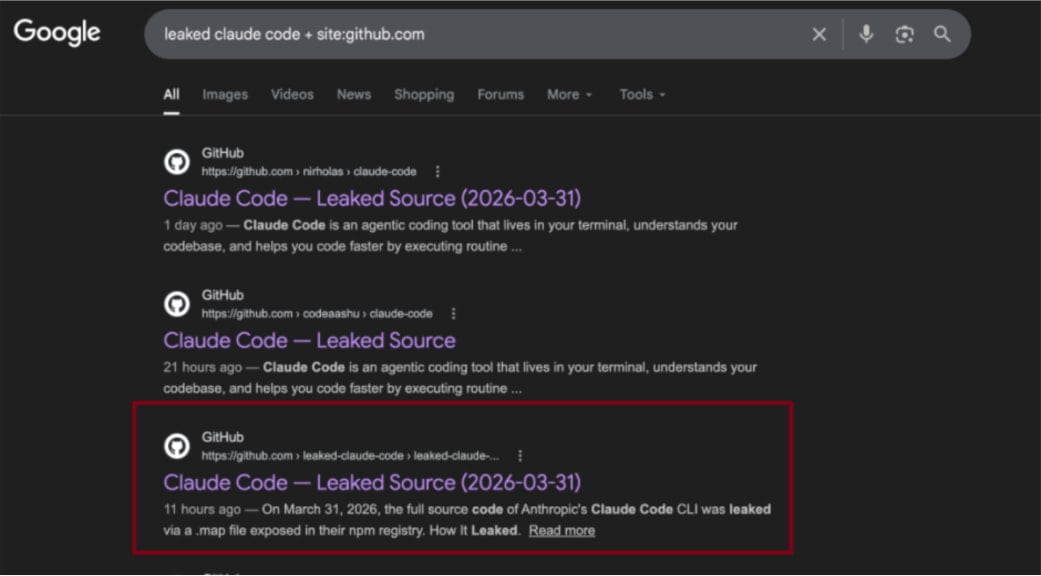
According to the researchers, curious users download a 7-Zip archive that contains a Rust-based executable named ClaudeCode_x64.exe. When launched, the dropper deploys Vidar, a commodity information stealer, along with the GhostSocks network traffic proxying tool.
Zscaler discovered that the malicious archive is updated frequently, so other payloads may be added in future iterations.
The researchers also spotted a second GitHub repository with identical code, but it instead shows a ‘Download ZIP’ button that wasn’t functional at the time of analysis. Zscaler estimates it is operated by the same threat actor who likely experiments with delivery strategies.
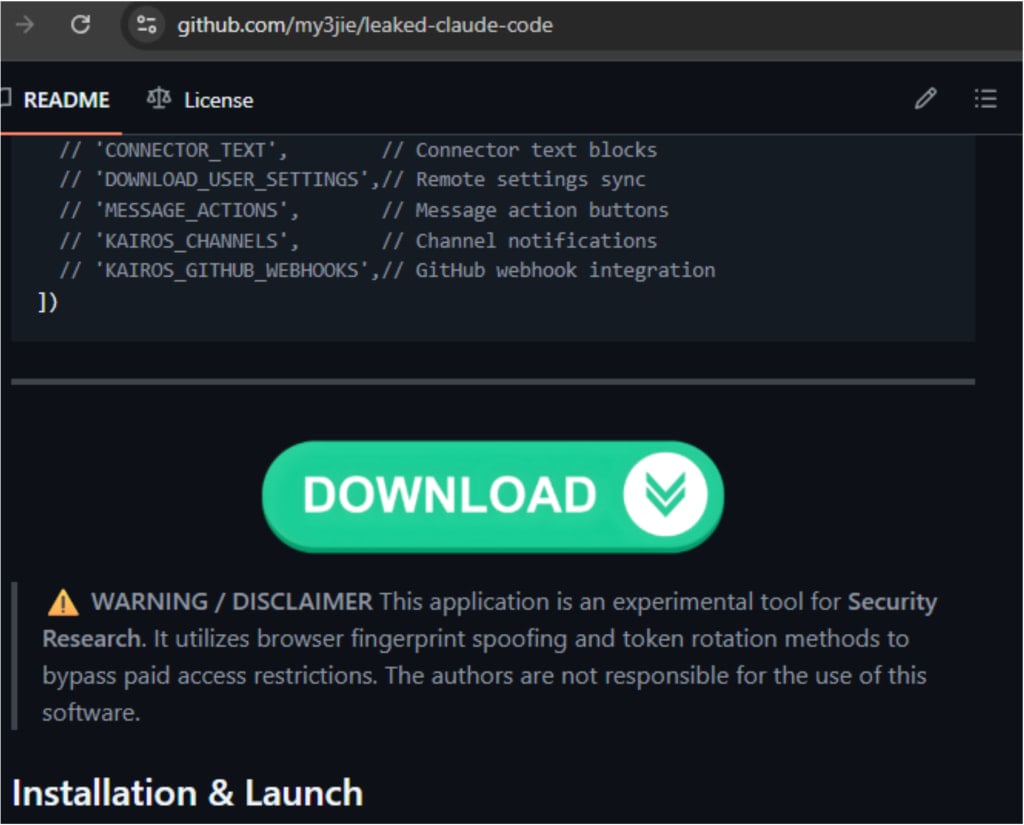
Despite the platform's defenses, GitHub has often been used to distribute malicious payloads disguised in various ways.
In campaigns in late 2025, threat actors targeted inexperienced researchers or cybercriminals with repositories claiming to host proof-of-concept (PoC) exploits for recently disclosed vulnerabilities.
Historically, attackers were quick to capitalize on widely publicized events in the hope of opportunistic compromises.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

Update: Revised story and title based on new information linking the attack with North Korean hackers.
The Drift Protocol lost at least $280 million after a threat actor took control of its Security Council administrative powers in a planned, sophisticated operation.
Blockchain intelligence firms Elliptic and TRM Labs linked the attacks to North Korean threat actors, based on multiple on-chain indicators consistent with DPRK tradecraft.
These include Tornado Cash usage, CarbonVote deployment timing (09:30 Pyongyang time), cross-chain bridging patterns, and rapid large-scale laundering, consistent with the Bybit hack.
The attacker leveraged durable nonce accounts and pre-signed transactions to delay execution and strike with accuracy at a chosen time, the platform explained.
Drift underlines that the hacker did not exploit any flaws in its programs or smart contracts, and no seed phrases have been compromised.
Drift Protocol is a DeFi trading platform built on the Solana blockchain that serves as a non-custodial exchange, giving users full control of their funds as they interact with on-chain markets.
As of late 2024, the platform claimed to have 200,000 traders, supporting total trading volumes of more than $55 billion and a daily peak of $13 million.
According to Drift's report, the heist was prepared between March 23 and 30, with the attacker setting up durable nonce accounts and obtaining 2/5 multisig approvals from Security Council members to meet the required threshold.
This enabled them to pre-sign malicious transactions that weren’t executed immediately.
On April 1st, the attacker performed a legitimate transaction and immediately executed the pre-signed malicious transactions, transferring admin control to themselves within minutes.
Having gained admin control, they introduced a malicious asset, removed withdrawal limits, and eventually drained funds.
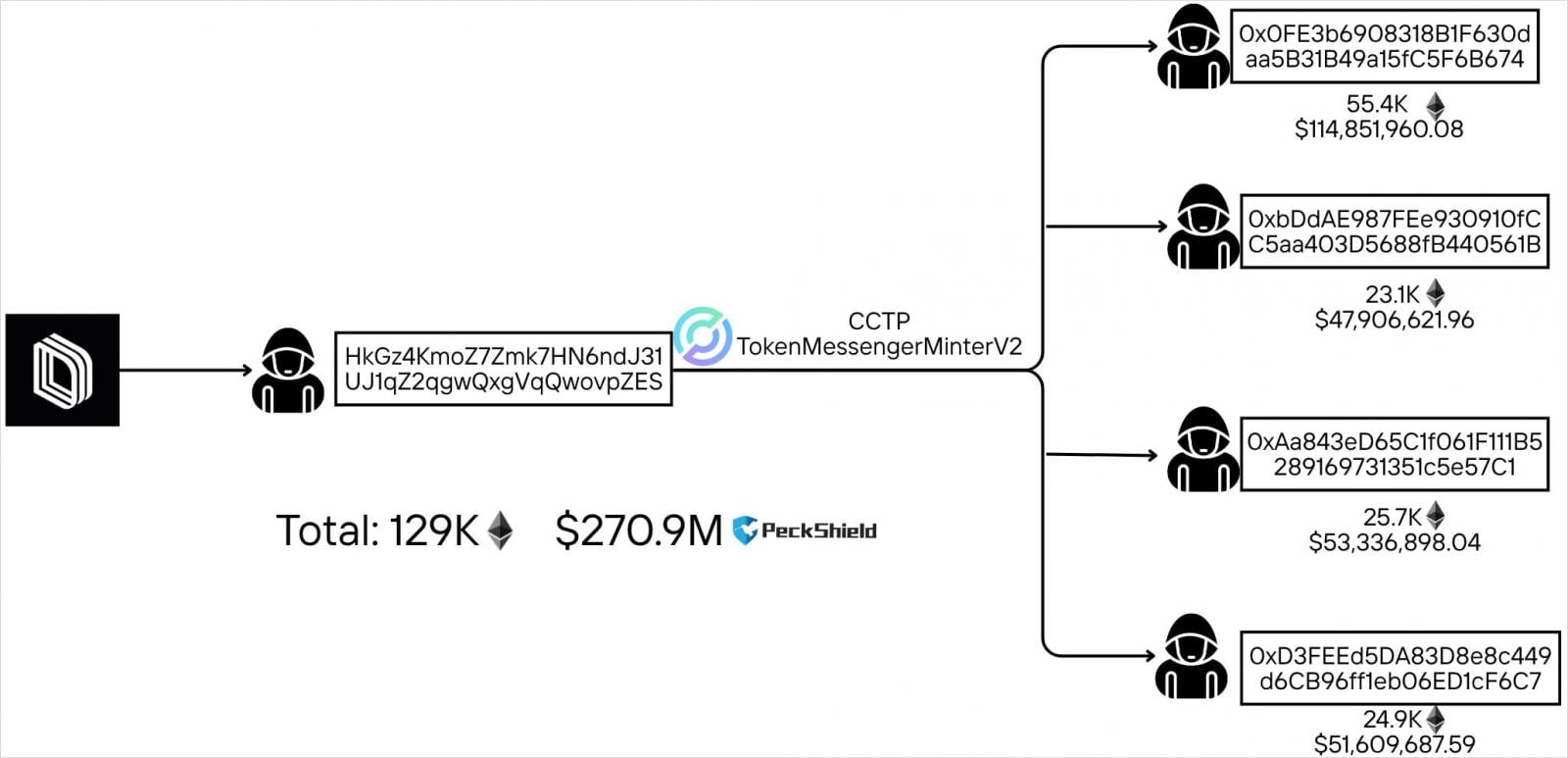
Drift Protocol estimates the losses at about $280 million, while blockchain tracking account PeckShieldAlert has calculated them at $285 million.
When unusual activity on the protocol was detected, Drift issued a public warning to users, stating that started an investigation and urging them not to deposit any funds until further notice.
As a result of the attack, borrow/lend deposits, vault deposits, and trading funds have been affected, and all protocol functions are now essentially frozen. Drift said DSOL is unaffected, and insurance fund assets are secured.
The platform is now working with security firms, cryptocurrency exchanges, and law enforcement authorities to trace and freeze the stolen funds.
Drift promised to publish a detailed post-mortem report in the coming days.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

Researchers warn that residential proxies used to route malicious traffic are a big problem for IP reputation systems, as there is no clear distinction between attackers and legitimate users.
This occurs because residential proxies are too short-lived, uninvolved, or systematically rotated, preventing defense systems from cataloging them in time.
Cybersecurity intelligence platform GreyNoise determined this after examining a massive dataset of 4 billion malicious sessions targeting the edge over a three-month period.
Roughly 39% of those sessions appear to originate from home networks, most certainly part of residential proxies, but 78% of them are invisible to reputation feeds.
“The data reveals a pattern that challenges a core assumption of network defense: that you can tell attackers from legitimate users by where the traffic comes from,” explains GreyNoise.
According to the company, most residential IPs are used once or twice, and then vanish, with attackers rotating them with others, keeping the pace at a level that reputation systems will not flag them.
About 89.7% of residential IPs are active in malicious operations for under a month, with only 8.7% lasting 2 months, and 1.6% persisting for 3 months.
Those that are kept alive for longer seem to carry a specialization according to the researchers, being SSH-focused and using Linux TCP stacks.
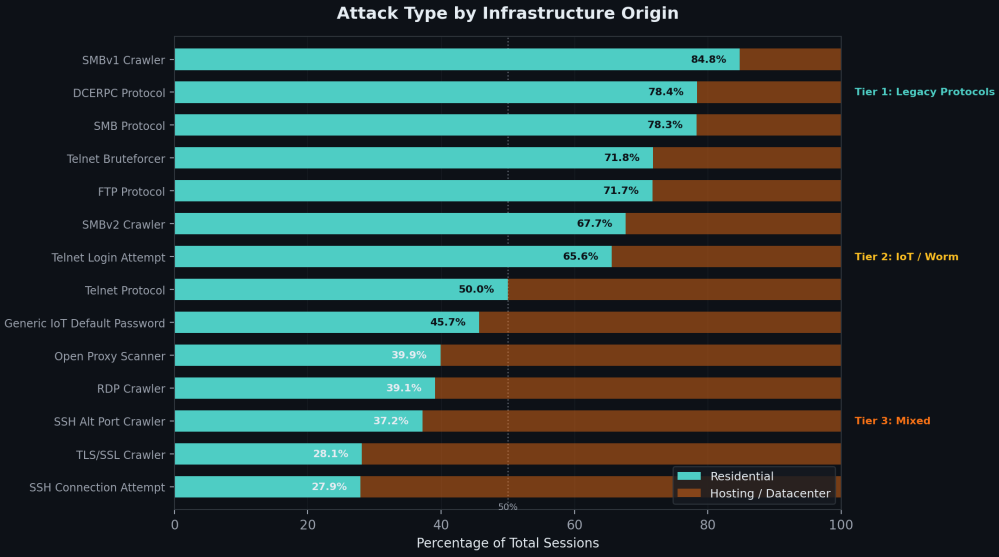
Diversity is another factor that complicates flagging and blocking, as GreyNoise’s data shows the residential IPs participating in attacks belong to 683 internet service providers.
Another reason for their stealthiness is that they are primarily used for network scanning and reconnaissance, with only 0.1% involved in actual exploits, the researchers say.
A small percentage (1.3%) targeted enterprise VPN login pages, while some limited cases also involved residential IPs to path traversal and credential stuffing attempts.
Regarding the source of the residential proxies, GreyNoise says China, India, and Brazil are major contributors, with traffic from the IPs following human sleep patterns, dropping by a third at night, when most people power off their devices.
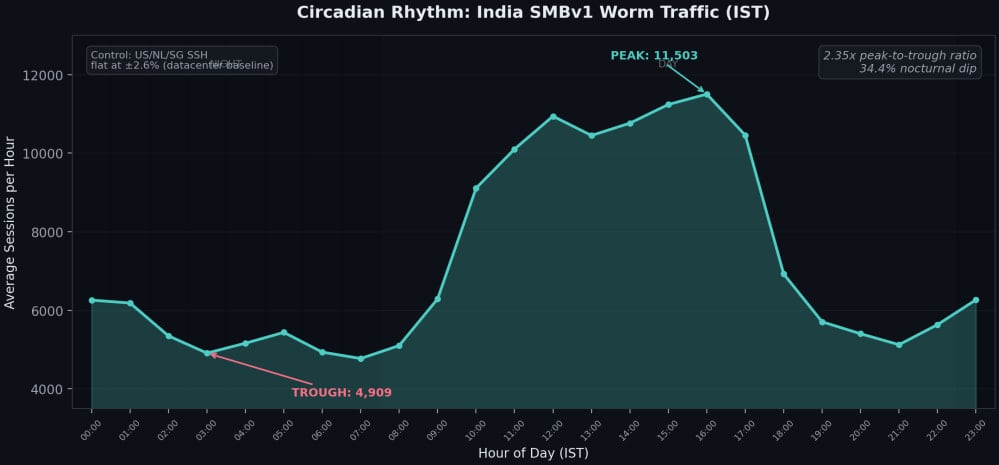
The researchers report that residential proxy traffic is generated by two distinct, non-overlapping ecosystems: IoT botnets and infected computers.
In cases involving the latter, the proxies come from SDKs in free VPNs, ad blockers, and similar apps, which enroll user devices in bandwidth-selling schemes.
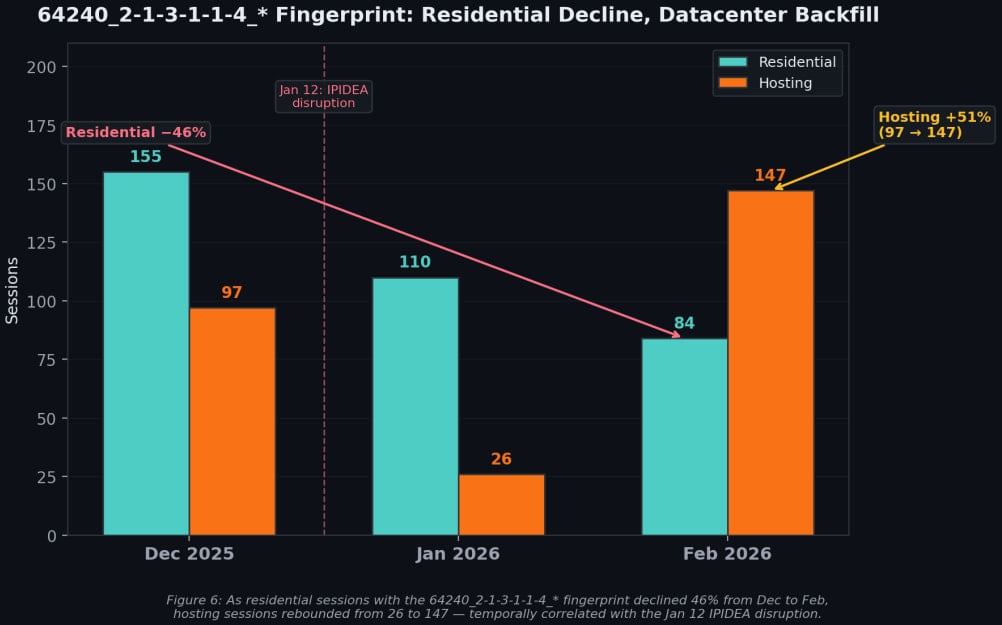
GreyNoise has also highlighted the resilience of these networks using the example of IPIDEA, one of the world’s largest residential proxy networks, which was recently disrupted by Google Threat Intelligence Group (GTIG) and partners.
The disruption reduced its proxy pool by roughly 40%, but in the period that followed, datacenter traffic increased, indicating that demand can be absorbed by others when needed and that lost capacity is quickly replaced.
GreyNoise says residential proxying evasion tactics require abandoning IP reputation as a primary signal and focusing instead on behavior.
The researchers suggest detecting sequential probing from rotating residential IPs, blocking clearly illegitimate protocols like SMB from ISP space, and tracking device fingerprints that survive IP rotation.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

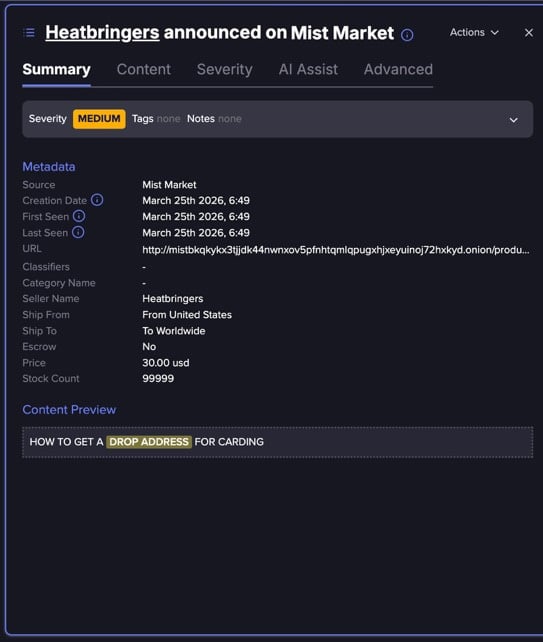
Fraud operations have expanded beyond traditional hacking techniques to include methods that exploit legitimate services and real-world infrastructure. By combining publicly available data, weak identity verification processes, and operational gaps, threat actors are building scalable fraud workflows that are both low-cost and difficult to detect.
A tutorial shared in a fraud-focused chat group and analyzed by Flare analysts provides step-by-step guidance on how to identify and exploit vacant residential properties to intercept sensitive mail, revealing a low-tech but highly effective method for enabling identity theft and financial fraud.
Unlike traditional cybercrime techniques that rely on malware, phishing kits, or network intrusions, the method outlined in this article focuses almost entirely on abusing legitimate services and physical-world logistics.
The approach blends open-source intelligence, postal service features, and fake identity fraud into a coordinated workflow designed to gain persistent access to victims’ mail.
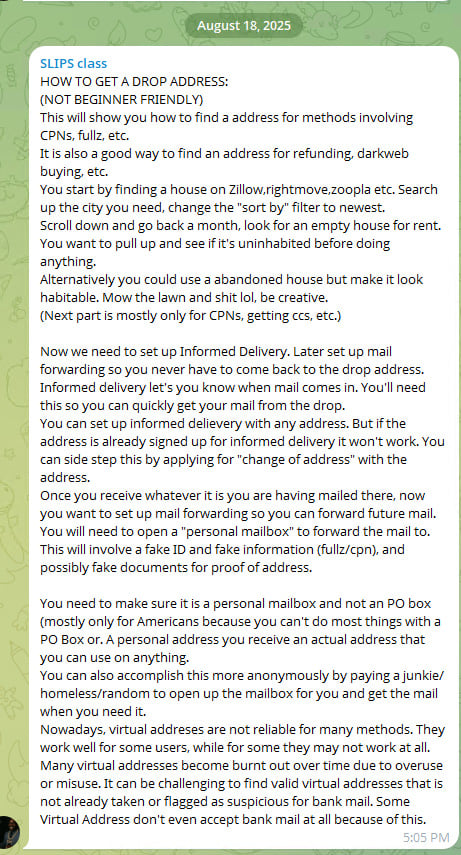
The tutorial begins with identifying so-called “drop addresses”, real residential properties that are temporarily unoccupied and can be used to receive mail without immediately alerting the rightful occupants.
Threat actors are instructed to search real estate platforms such as Zillow, Rightmove, or Zoopla, filtering for recently listed rental properties. By focusing on newly available listings, attackers increase the likelihood that the property is vacant or between tenants.
The guidance further suggests reviewing older listings to identify homes that have remained unoccupied for extended periods, increasing their reliability as drop locations.
In some cases, threat actors even recommend physically maintaining abandoned properties to make them appear occupied, reducing the risk of drawing attention while using the address for fraudulent purposes.
Threat actors share fraud playbooks, stolen credentials, and fake document services across dark web forums and Telegram channels.
Flare monitors these sources continuously, so you can detect exposure before it enables account takeovers, mail fraud, or identity theft.
Keep up with threat actors for freeOnce a suitable address is identified, the next phase involves utilizing legitimate digitalized postal services for discovery and monitoring of incoming mail.
Informed Delivery, for instance, is a free service that provides residential consumers with digital previews of their incoming letter-sized mail and tracks package deliveries.
By registering these services for the selected address, attackers can monitor incoming correspondence remotely, allowing them to identify valuable items such as financial documents, credit cards, or verification letters before physically accessing the mailbox.
This transforms mail delivery into a form of intelligence gathering, enabling more targeted and efficient fraud.
If the address is already registered, the tutorial references change-of-address requests as a way to regain control over mail delivery. These services are designed for legitimate users relocating their residence and are widely available through postal systems such as USPS.
For example, users can submit a permanent or a temporary Change of Address (COA) request online or in person, enabling mail to be forwarded to a new location for periods ranging from several weeks up to 12 months.
Additional services, such as Premium Forwarding, can consolidate and redirect all incoming mail on a recurring basis.
While these mechanisms include identity verification safeguards such as requiring a small online payment tied to a billing address or presenting a valid photo ID in person, the tutorial suggests that actors perceive these controls as potentially insufficient or inconsistently enforced.
In particular, the ability to submit forwarding requests remotely, combined with the reliance on address-linked verification rather than strong identity binding, may create opportunities for abuse if supporting identity information is compromised or fabricated.
As a result, control over mail delivery may, in some cases, be reassigned without direct interaction with the legitimate resident, turning a service intended for convenience into a potential vector for unauthorized redirection.
At this stage, the operation moves beyond passive targeting and into active monitoring, providing attackers with visibility that significantly increases the success rate of downstream fraud.
After confirming that valuable mail is being delivered, the workflow shifts toward establishing long-term access through mail forwarding services.
Actors are instructed to create personal mailbox accounts that allow them to redirect all incoming mail from the drop address to a separate location under their control.
Because these services typically require identity verification, attackers rely on fake identities, forged documents, or purchased personal data to complete the process.
This marks a critical transition from opportunistic interception to persistent access. Once mail forwarding is in place, attackers no longer need to revisit the physical location, reducing exposure while maintaining continuous access to sensitive information.
The use of fake identities, often involving fabricated personal details or Credit Privacy Numbers (CPNs), demonstrates how this technique integrates with broader fraud ecosystems.
Rather than operating in isolation, drop address abuse becomes one component in a larger pipeline that can support account takeovers, credit fraud, and refund scams.
In practice, these fake identities can be used to register mailbox services, submit forwarding requests, or receive sensitive financial correspondence tied to victim accounts.
This allows actors to bridge the gap between digital compromise and real-world access, enabling them to complete verification steps, intercept authentication materials, or establish new accounts under assumed identities.
As a result, control over a physical address can become an important step in fraud operations that depend on both identity credibility and access to legitimate communication channels.
The method outlined in the tutorial reflects a broader evolution in fraud operations, where digital intelligence gathering is combined with physical-world manipulation.
In addition to leveraging online platforms and postal services, actors also describe using individuals (sometimes recruited from vulnerable populations) to physically access mailboxes or collect delivered items.
This introduces a human layer into the operation, allowing attackers to outsource risk and further distance themselves from direct involvement.
The activity described in the tutorial reflects a broader rise in mail-enabled fraud documented in recent reporting. According to U.S. Postal Inspection Service–related data, reports of mail theft have increased significantly in recent years, with theft from mail receptacles rising by 139% between 2019 and 2023.
Financially, the impact is substantial, with mail theft schemes linked to hundreds of millions of dollars in suspicious activity tied to check fraud.
At the same time, abuse of postal redirection services, similar to the technique referenced in the tutorial, has also grown, with change-of-address fraud increasing sharply year-over-year. Together, these trends highlight how control over physical mail has become valuable.
At the same time, the tutorial acknowledges operational challenges. Virtual addresses and commonly reused locations are increasingly flagged by financial institutions, suggesting that defenders are beginning to incorporate address-based risk signals into their detection models.
As a result, actors emphasize the importance of finding “clean” residential addresses that have not yet been associated with fraudulent activity.
Together, these elements illustrate a fraud model that is not driven by technical sophistication, but by coordination, adaptability, and the strategic use of legitimate systems.
While this may look like an isolated tutorial, this is part of a broader phenomenon or tutorials on how to find physical drop address, some are for free and others are paid for.
The emergence of these techniques underscores a growing challenge for organizations: many of the systems being abused: real estate platforms, postal services, and identity verification processes, exist outside the scope of traditional cybersecurity defenses.
As fraud operations continue to evolve, detection increasingly depends on correlating signals across domains, including address usage patterns, mail forwarding activity, and identity inconsistencies. Without this broader visibility, attacks that rely on legitimate services rather than technical exploits may continue to evade conventional security controls.
Learn more by signing up for our free trial.
Sponsored and written by Flare.
html Sponsored by Flare 1775136791 New Progress ShareFile flaws can be chained in pre-auth RCE attacks https://www.bleepingcomputer.com/news/security/new-progress-sharefile-flaws-can-be-chained-in-pre-auth-rce-attacks/
Two vulnerabilities in Progress ShareFile, an enterprise-grade secure file transfer solution, can be chained to enable unauthenticated file exfiltration from affected environments.
Progress ShareFile is a document sharing and collaboration product typically used by large and mid-sized companies.
Such solutions are an attractive target for ransomware actors, as previously seen in Clop data-theft attacks exploiting bugs in Accellion FTA, SolarWinds Serv-U, Gladinet CentreStack, GoAnywhere MFT, MOVEit Transfer, and Cleo.
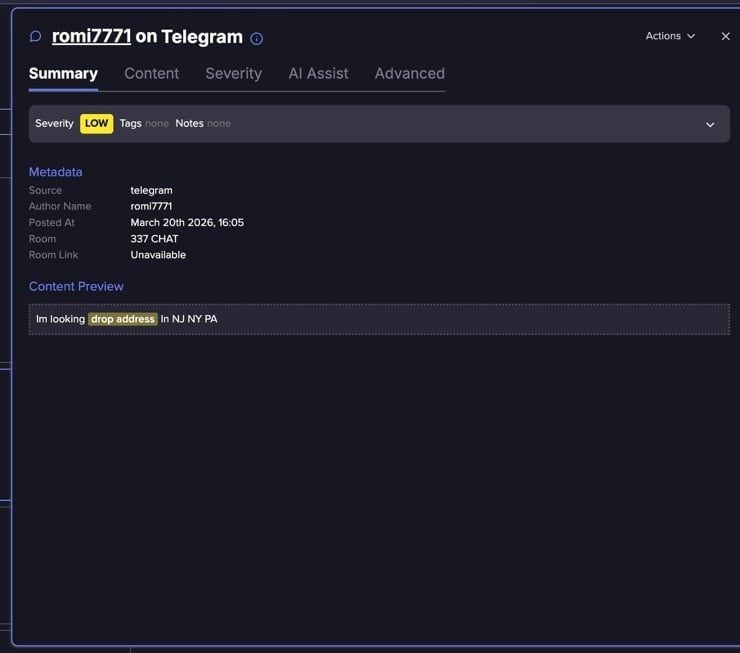
Researchers at offensive security company watchTowr discovered an authentication bypass (CVE-2026-2699) and a remote code execution (CVE-2026-2701) in the Storage Zones Controller (SZC) component present in branch 5.x of Progress ShareFile.
SZC gives customers more control over their data by allowing them to store it on their infrastructure (either on-prem or in a third-party cloud provider) or on the Progress systems.
Following watchTowr's responsible disclosure, the problems have been addressed in Progress ShareFile 5.12.4, released on March 10.
In a report today, watchTowr researchers explain that the attack begins by exploiting the authentication bypass issue, CVE-2026-2699, which gives access to the ShareFile admin interface due to improper handling of HTTP redirects.
Once inside, an attacker can modify Storage Zone configuration settings, including file storage paths and security-sensitive parameters such as the zone passphrase and related secrets.
By exploiting the second flaw, CVE-2026-2701, attackers can obtain remote code execution on the server by abusing file upload and extraction functionality to place malicious ASPX webshells in the application’s webroot.
The researchers note that, for the exploit to work, attackers must generate valid HMAC signatures and extract and decrypt internal secrets. However, these are achievable after exploiting CVE-2026-2699 due to the ability to set or control passphrase-related values.
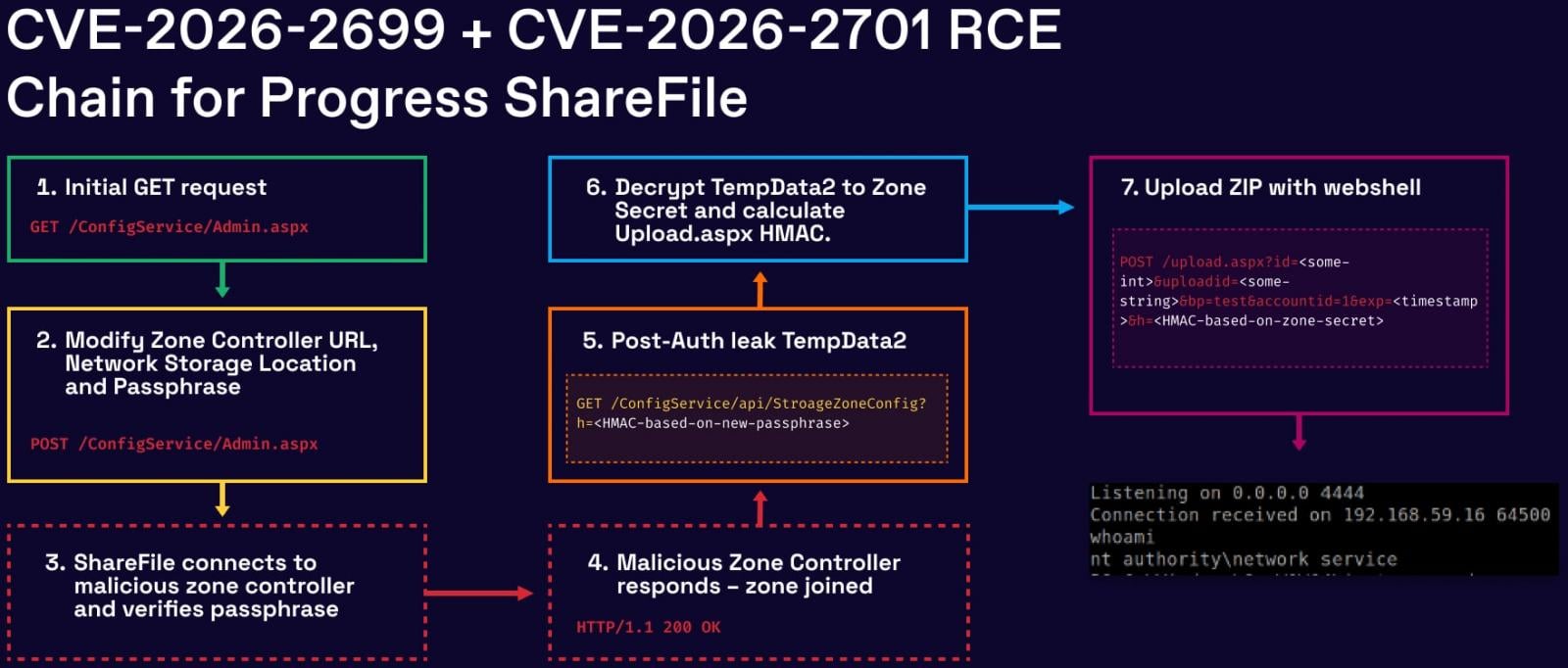
By watchTowr's scans, there are about 30,000 Storage Zone Controller instances exposed on the public internet.
The ShadowServer Foundation currently observes 700 internet-exposed instances of Progress ShareFile, most of which are located in the United States and Europe.
watchTowr discovered the two flaws and reported them to Progress between February 6 and 13, and the full exploit chain was confirmed on February 18 for Progress ShareFile 5.12.4. The vendor released security updates in version 5.12.4, released on March 10.
Although no active exploitation in the wild has been observed as of writing, systems running vulnerable versions of ShareFile Storage Zone Controller should be patched immediately, as the public disclosure of the chain is likely to entice threat actors.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

Stryker Corporation, one of the world's leading medical technology companies, says it's fully operational three weeks after many of its systems were wiped out in a cyberattack claimed by the Iranian-linked Handala hacktivist group.
The Fortune 500 medtech giant has over 53,000 employees, makes a wide range of products (including neurotechnology and surgical equipment), and reported global sales of $22.6 billion in 2024.
The attackers began wiping Stryker's systems on March 11, claiming they had stolen 50 terabytes of data before wiping nearly 80,000 devices early that morning, using a new Global Administrator account created after compromising a Windows domain admin account.
After the attack was disclosed, CISA and Microsoft released guidance on securing Intune and hardening Windows domains to block similar attacks, while the FBI seized two websites used by the Handala hackers.
On Wednesday, Stryker announced that it had restored enough systems to return to pre-attack operational levels and that production would quickly reach full capacity.
"As of this week, we are fully operational across our global manufacturing network. Production is moving rapidly toward peak capacity with discipline and stability, supported by restored commercial, ordering and distribution systems," Stryker said.
"Overall product supply remains healthy, with strong availability across most product lines, as we continue to meet customer demand and support patient care."
"Our work continues around the clock in close partnership with third‑party cybersecurity experts, relevant government agencies and industry partners as our investigation progresses, reflecting a shared commitment to protecting the healthcare ecosystem and supporting ongoing recovery efforts," it added.
This comes after the company said on March 23 that its teams were prioritizing the restoration of systems that directly support customer, ordering, and shipping operations.
Although it was initially believed the attackers hadn't used any malicious tools during the breach, Stryker also revealed that security experts who helped with the investigation found a malicious file that helped the attackers hide malicious activity while inside the company's network.
Handala (also known as Handala Hack Team, Hatef, Hamsa) surfaced in December 2023 as an Iranian-linked and pro-Palestinian hacktivist operation that has been targeting Israeli organizations with Windows and Linux data-wiping malware.
The hacktivist group has been linked to Iran's Ministry of Intelligence and Security (MOIS) and is also known for leaking sensitive data stolen from victims' compromised systems.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

Cisco has released security updates to address several critical and high-severity vulnerabilities, including an Integrated Management Controller (IMC) authentication bypass that allows attackers to gain Admin access.
Also known as CIMC, Cisco IMC is a hardware module embedded on the motherboard of Cisco servers that provides out-of-band management (even if the operating system is powered off or crashed) for UCS C-Series and E-Series servers via multiple interfaces, including XML API, web (WebUI), and command-line (CLI).
Tracked as CVE-2026-20093, the vulnerability was found in the Cisco IMC password change functionality and can be remotely exploited by unauthenticated attackers to bypass authentication and access unpatched systems with Admin privileges.
"This vulnerability is due to incorrect handling of password change requests. An attacker could exploit this vulnerability by sending a crafted HTTP request to an affected device," Cisco explained on Wednesday.
"A successful exploit could allow the attacker to bypass authentication, alter the passwords of any user on the system, including an Admin user, and gain access to the system as that user."
While Cisco's Product Security Incident Response Team (PSIRT) has yet to find evidence of in-the-wild exploitation or a proof-of-concept exploit code, the company "strongly recommends that customers upgrade to the fixed software" as there are no workarounds to temporarily mitigate this security flaw.
This week, Cisco has also released patches for a critical Smart Software Manager On-Prem (SSM On-Prem) vulnerability (CVE-2026-20160) that could enable threat actors without privileges to gain remote code execution (RCE) on vulnerable SSM On-Prem hosts.
Attackers can exploit the CVE-2026-20160 vulnerability by sending a crafted request to the exposed service's API, allowing them to execute commands on the underlying OS with root-level privileges.
Earlier this month, Cisco patched a maximum-severity RCE vulnerability (CVE-2026-20131) in the Secure Firewall Management Center (FMC) that the Interlock ransomware gang exploited in zero-day attacks. CISA has also added CVE-2026-20131 to its catalog of flaws abused in the wild, ordering federal agencies to secure their systems within three days.
More recently, BleepingComputer reported that Cisco's internal development environment was breached using credentials stolen during the recent Trivy supply chain attack.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

Microsoft is investigating a known issue that prevents some Classic Outlook users from sending emails via Outlook.com.
Affected users are being warned that their message hasn't reached some intended recipients, and they will encounter this problem more often when the Outlook.com account they use to send email is an Outlook profile linked to another Exchange account.
"This message could not be sent. Try sending the message again later or contact your network administrator," the non-delivery report (NDR) error displayed when sending or replying to emails reads.
"You do not have the permission to send the message on behalf of the specified user. Error is [0x80070005-0x0004dc-0x000524]."
Microsoft added that another condition that may trigger these errors is that the sender's account has an Exchange Online mail contact with the same SMTP address.
%20error.jpg)
While investigating this issue and still looking for a fix, the Outlook team shared several workarounds that may help affected customers temporarily mitigate the issue.
Microsoft recommends removing the M365 account Address Book so that the Outlook client does not check it when sending emails, hiding the Outlook.com contact from the Microsoft 365 account Global Address List (GAL).
Other alternatives include creating a new classic Outlook profile that includes only the account receiving NDR errors, and using the New Outlook client or Outlook.com on the web to send email from the affected account.
Over the last two weeks, Microsoft fixed two other known issues, including one that caused Classic Outlook to crash when enabling the Microsoft Teams Meeting Add-in and another that triggered 0x800CCC0F and 0x80070057 errors when synchronizing Gmail and Yahoo accounts.
Microsoft is also investigating known bugs that cause "Can't connect to the server" errors when creating groups if Exchange Web Services (EWS) is enabled for the tenant, and that make the mouse pointer disappear for some users in Classic Outlook, OneNote, and other Microsoft 365 apps.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.

Internet threat-monitoring non-profit Shadowserver has found over 14,000 BIG-IP APM instances exposed online amid ongoing attacks exploiting a critical-severity remote code execution (RCE) vulnerability.
BIG-IP APM (short for Access Policy Manager) is F5's centralized access management proxy solution designed to help admins secure access to their organizations' networks, cloud, applications, and application programming interfaces (APIs).
This 5-month-old flaw (tracked as CVE-2025-53521) was disclosed in October as a denial-of-service (DoS) vulnerability and was reclassified as an RCE bug over the weekend.
"Due to new information obtained in March 2026, the original vulnerability is being re-categorized to an RCE. The original CVE remediation has been validated to address the RCE in the fixed versions. We have learned that this vulnerability has been exploited in the vulnerable BIG-IP versions," F5 warned in a Sunday advisory update.
Attackers without privileges are exploiting this security issue to gain remote code execution on unpatched BIG-IP APM systems with access policies configured on a virtual server.
While there is no information on how many BIG-IP APM instances exposed on the Internet have a vulnerable configuration, Internet threat-monitoring non-profit Shadowserver said on Wednesday that it now tracks over 17,100 IPs with BIG-IP APM fingerprints.
More than 14,000 BIG-IP APM systems remain exposed to CVE-2025-53521 attacks according to Shadowserver's data, even though the U.S. Cybersecurity and Infrastructure Security Agency (CISA) ordered federal agencies to secure their BIG-IP APM systems by midnight on Monday (after adding the vulnerability to its list of actively exploited flaws on Friday).
F5 has also shared published indicators of compromise (IOCs) and advised defenders to check the disks, logs, and terminal history of BIG-IP devices for signs of malicious activity. It also provides guidance on the measures to take after detecting evidence of compromise, including rebuilding the affected systems from scratch.
"If customers do not know exactly when the system was compromised, user configuration set (UCS) backups may have been created after the compromise occurred," the company said.
"F5 strongly recommends that customers rebuild the configuration from a known good source because UCS files from compromised systems can contain persistent malware."
As a Fortune 500 technology giant, F5 provides cybersecurity, application delivery networking (ADN), and other services to over 23,000 customers, including 48 Fortune 50 companies.
In recent years, BIG-IP vulnerabilities have been targeted by both nation-state and cybercrime threat groups to breach corporate networks, hijack devices, deploy data-wiping malware, map internal servers, and steal sensitive data.
\tAutomated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.